Complete DDoS Protection: L3, L4, and L7 Attacks
When you hear "Site is under DDoS", it's just a symptom. To treat the disease, you need to understand at which OSI model layer the attack is happening. Protection that saves from UDP flood (L3) will be useless against slow XML parsing (L7). At NineLab, we use defense in depth.
Attack Anatomy by OSI Layers
Imagine your server as a medieval castle. The enemy can try to smash the gates with a battering ram (L3/L4) or pretend to be a messenger and poison the well (L7).
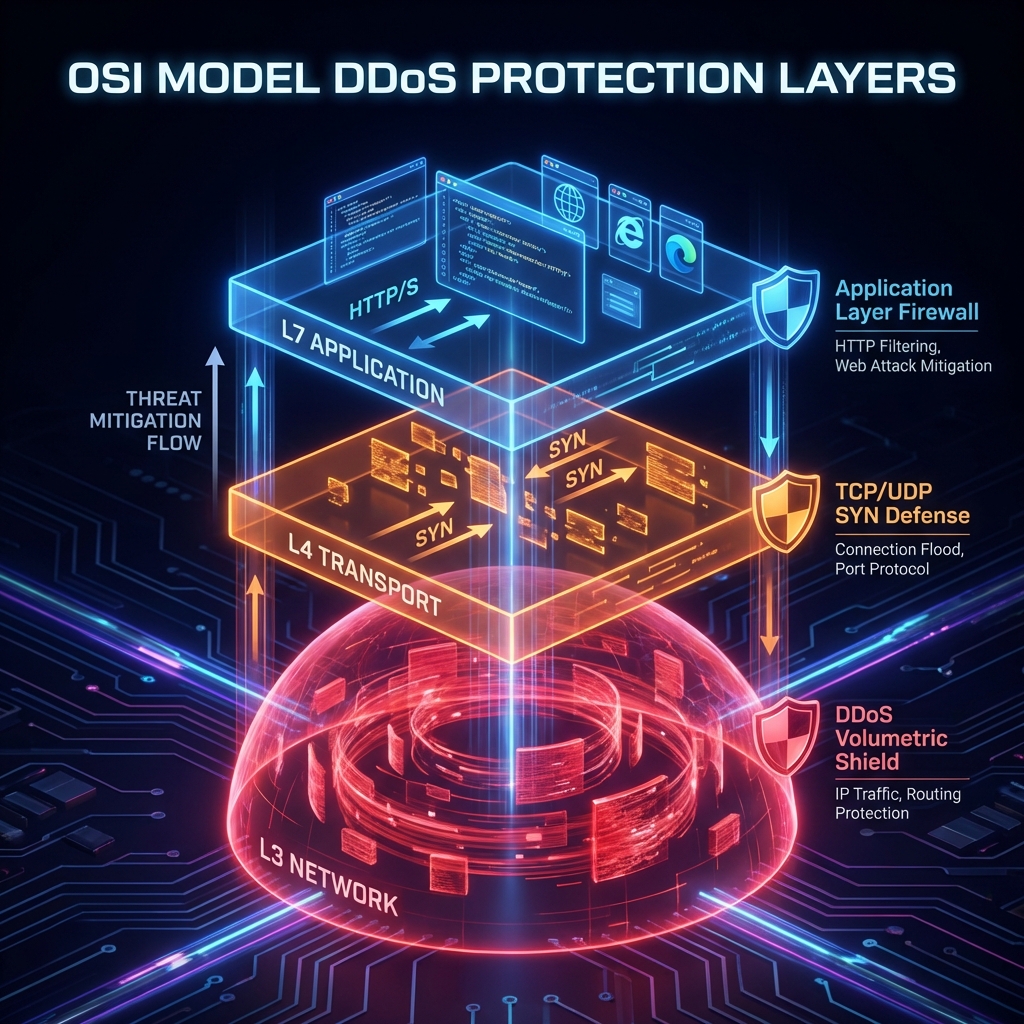
Fig 1. Layered Protection by OSI Model
L3: Network Layer
Goal: Clog the communication channel ("pipe") so legitimate packets simply can't get through.
- Attack Types: UDP Flood, ICMP Flood, IP Fragmentation.
- Protection: Only at the ISP level or Scrubbing Centers (Qrator, Cloudflare). A local firewall won't help here — the channel will go down before traffic reaches the server.
L4: Transport Layer
Goal: Exhaust the server's connection table resources (RAM/CPU).
- Attack Types: SYN Flood (attacker sends requests to open a connection but doesn't complete them).
- Protection: SYN Cookies, limiting the number of connections from one IP.
L7: Application Layer
Goal: Overload the application logic (CPU/Database).
- Attack Types: HTTP Flood, Slowloris, heavy SQL queries.
- Protection: WAF, behavioral analysis, Challenge-Response (JS/Captcha), caching.
NineLab Strategy: "Security Onion"
We don't believe in "silver bullets". Effective protection is always multi-layered:
- Outer Perimeter: BGP Anycast network disperses L3/L4 attacks globally.
- Entry Control: WAF filters 99% of bots at L7.
- Core: Optimized code and Auto-Scaling digest the leaked traffic.
Summary: Protection is not a product, it's an architecture. If you are protected only at L3, you will be "killed" at L7. If only at L7 — your channel will be clogged at L3. Close all doors.
Related services
FAQ for this topic
VPN protects transport/perimeter; Zero Trust adds continuous checks of identity, device, and context per request.
Pentest is a snapshot; without patching, WAF/limits, and anomaly monitoring, risk returns quickly.
In layers: provider, edge, app rate limits and queues—plus rehearsals under controlled load, not unlawful third-party attacks.
Minimize fields, retention, access, and encryption; align with your DPO and policies.
Want to apply this in practice?
Tell us about your system — we’ll propose a work plan and the metrics worth fixing in an SLA/SLO.
Related articles
Security in 2026: Why VPNs are Obsolete and You Need Zero Trust
Traditional VPNs can no longer cope with modern threats. We explain why corporate networks must transition to Zero Trust Architecture (ZTA).
Read ArticleHow NineLab Built a Corporate SD-WAN Platform
Experience building a reliable and secure network infrastructure: VLESS/Reality encryption, load balancing, fault tolerance, and 900 Mbit/s on a standard VDS.
Read ArticleCorporate VPN: Why Public Services Are Dangerous
Corporate VPN vs consumer VPNs: data-leak and compliance risks of public clients, control over keys and logging, and why a dedicated, auditable stack matters for remote work in 2026.
Read Article