Security in 2026: Why VPNs are Obsolete and You Need Zero Trust
The world has finally transitioned to a hybrid work format. Your employees connect to corporate resources from coworking spaces in Bali, from home networks, or through public Wi-Fi at airports. Under these conditions, protecting the corporate network becomes task number one. For many years, VPN (Virtual Private Network) remained the de facto standard for remote access. But in 2026, we confidently declare: relying solely on a VPN means leaving the front door to your infrastructure wide open.
In this article, Nine Lab engineers analyze why classic VPN solutions are outdated, what their fundamental vulnerability is, and why transitioning to Zero Trust Architecture (ZTA) is the only way to guarantee business security.
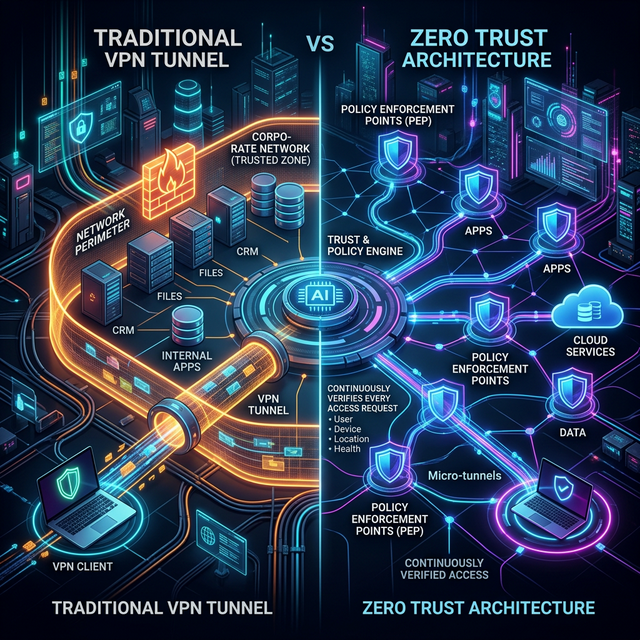
From traditional VPN tunnels to continuous trust verification in ZTA
The Illusion of Security: Why VPN No Longer Saves the Day?
Traditional VPN is based on the concept of a "secured perimeter." Imagine a medieval castle surrounded by a high wall and a moat. A VPN creates a secret underground tunnel across this moat directly into the courtyard.
Once a user enters the VPN tunnel (passes primary authentication), they are inside the secured perimeter. And here lies the main problem: the system inherently trusts anyone inside.
Why the "Trust but Verify" model is dangerous:
- Single Point of Failure. If an attacker steals an employee's credentials (e.g., via phishing) and connects to the VPN, they gain almost unlimited access to the internal network. The hacker can move laterally from server to server, scanning ports and downloading databases.
- Uncontrolled Devices. Your CRM is accessed from an employee's personal laptop infected with malware. The VPN carefully lays a secure tunnel for viruses straight to your corporate servers. Perimeter defense does not check the "health" of the device.
- Over-Privileged Access. A sales manager only needs access to the CRM and email, but through the corporate VPN, they can also see developer test environments, Jenkins, and Grafana on the network.
For modern distributed systems, microservices, and cloud infrastructures, the "high wall" model simply no longer works.
What is Zero Trust Architecture (ZTA)?
The Zero Trust concept is built on a simple and strict rule: Never Trust, Always Verify.
In ZTA, there is no such thing as a "trusted internal network." It doesn't matter whether a request originates inside the corporate office or from a cafe on the other side of the world — every connection request is treated as a potential threat.
The Three Pillars of Zero Trust Architecture:
- Continuous Authentication and Authorization. Access is granted not just once upon entering the "tunnel," but continuously, for every single action or request. Verification includes: user identity, device health state, location, time of request, and even behavioral patterns.
- Principle of Least Privilege. A user receives access to exactly the part of the system and only for the duration necessary to perform their job. Not a byte more.
- Microsegmentation. The entire network is broken down into isolated segments. Unlike a flat VPN network, even if a hacker gains one-time access to an employee's email, they won't be able to "jump" to an adjacent segment containing financial reports or customer databases.
VPN vs Zero Trust: What is the Key Difference?
1. Trust:
- Traditional VPN: Trusts after entry ("it's safe inside the walls").
- Zero Trust (ZTA): No default trust.
2. Access Level:
- Traditional VPN: Grants access to the entire subnet or a broad pool of IPs.
- Zero Trust (ZTA): Grants strict access only to specific applications.
3. Context Check:
- Traditional VPN: Usually requires only login/password + 2FA at the start of the session.
- Zero Trust (ZTA): Continuous verification of every request (who, from what device, from where, why).
4. Lateral Movement:
- Traditional VPN: Possible. Once inside, hackers can easily expand their attack within the network.
- Zero Trust (ZTA): Blocked due to strict macro- and micro-segmentation.
5. Compromised Device Protection:
- Traditional VPN: Weak. Viruses can easily pass through the tunnel from personal devices.
- Zero Trust (ZTA): High. The Policy Engine continuously checks device "health" and instantly blocks it in case of a threat.
Nine Lab's Experience: From VPN Tunnels to Zero Trust Orchestration
The Nine Lab team has extensive experience in designing network security and VPN orchestration for 50,000+ nodes. We know exactly how tunnels work "under the hood."
In our large-scale infrastructure projects — whether parsing SEO metrics from thousands of IPs, heavily loaded IoT systems (up to 25 million transactions), or blockchain-based referral programs — we utilize ZTA principles.
How we implement security for client projects:
- Abandoning static keys. We use dynamic rotation of keys and access tokens.
- Identity-Aware Proxy (IAP). All requests to internal applications pass through a secure gateway that does not expose application IP addresses to the outside. DDoS attack protection operates at the level of this gateway (L7 protection).
- Deep security audits. We design the architecture so that the compromise of one service does not lead to the downfall of others (Microservices + Network Policies).
- Observability. All requests (successful and rejected) are logged and analyzed in real-time.
How to Start the Transition to ZTA in Your Company?
Implementing Zero Trust is not installing a "magic program." It is an evolution of processes and architecture. But you need to start right now:
- Conduct a technical inventory. Understand where your critical data resides, who has access to it, and how connections are made.
- Implement strict SSO (Single Sign-On) and MFA (Multi-Factor Authentication). This is the basic hygiene minimum.
- Start microsegmentation with the most critical assets. Isolate payment systems and databases from the rest of the network using strict orchestration rules.
- Limit VPN access. If a VPN is still necessary, switch routing policies from "allow entire network" to "allow only 3 specific service IPs" for each group of remote workers.
Don't Wait for an Incident
Most companies only realize that "VPN wasn't enough" when they read an incident report from forensic specialists.
Nine Lab specializes in developing reliable and secure solutions for businesses. If you realize that your company's current IT infrastructure has become a bottleneck or poses security risks — contact us.
We will conduct a comprehensive security audit of your site and infrastructure, design an L7 attack protection system, and help smoothly transition your company to modern Zero Trust standards.
Your business deserves an infrastructure you can trust 100%.
Related services
FAQ for this topic
VPN protects transport/perimeter; Zero Trust adds continuous checks of identity, device, and context per request.
Pentest is a snapshot; without patching, WAF/limits, and anomaly monitoring, risk returns quickly.
In layers: provider, edge, app rate limits and queues—plus rehearsals under controlled load, not unlawful third-party attacks.
Minimize fields, retention, access, and encryption; align with your DPO and policies.
Want to apply this in practice?
Tell us about your system — we’ll propose a work plan and the metrics worth fixing in an SLA/SLO.
Related articles
How NineLab Built a Corporate SD-WAN Platform
Experience building a reliable and secure network infrastructure: VLESS/Reality encryption, load balancing, fault tolerance, and 900 Mbit/s on a standard VDS.
Read ArticleCorporate VPN: Why Public Services Are Dangerous
Corporate VPN vs consumer VPNs: data-leak and compliance risks of public clients, control over keys and logging, and why a dedicated, auditable stack matters for remote work in 2026.
Read ArticleComplete DDoS Protection: L3, L4, and L7 Attacks
DDoS across OSI layers: how L3, L4, and L7 attacks differ, why a single appliance is rarely enough, and how to combine scrubbing, WAF, and app architecture for resilient services.
Read Article